RITSEC CTF 2019 – Write Up
Between Nov 15 – Nov 18, I participated in my second CTF challenge, the RITSEC CTF. The overall competition was challenging in numerous ways but very rewarding. Our team of 3, including a team member participating in his first CTF, finished 236/900 teams. This CTF allowed me to explore new tools to use for challenge solving, including new cipher decoding tools and Linux commands. For this competition, I wanted to gain more experience in cryptography and concentrated my attention on that category. The following writeups focus on the challenges I solved.
1 – Gold Bug Cipher
2 – German Cipher
3 – ROT47
Gold Bug Cipher
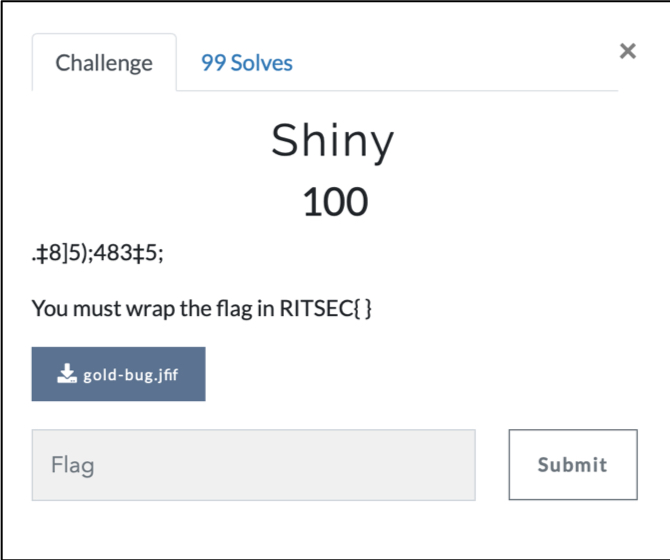
Title– Shiny
Category– Cryptography
Description– .‡8]5);483‡5;
You must wrap the flag in RITSEC{ }
Competition– RITSEC 2019
1. The challenge provided the following hint of a golden bug in the file format of a jfif.
2. My first thought to this challenge was to open a terminal shell and run a file command
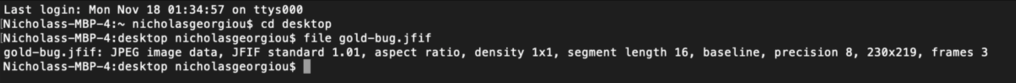
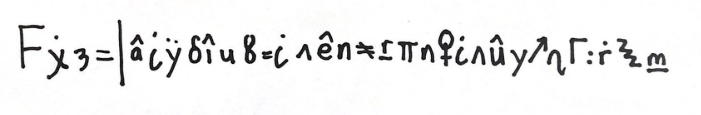
3. From this I was able to find the file format of the file (jpg) and change the file extension to a jpg which gave the following image.

4. After receiving this image, I searched for this symbol ‘‡ (double dagger)’. From this I googled ‘double dagger cipher’. The first result was a called the ‘gold-bug cipher’ which provided me with a pattern match to the image.
5. Using the gold-bug cipher online decoder, I entered the cryptic code given to me and received the following result ‘POEWASTHEGOAT’. Wrapping this I received the final flag RITSEC{poewasthegoat}. NOTE: entering as capitals didn’t work and therefore it had to be inserted as lowercase.
German Cipher
Title– Initiation
Category– Cryptography
Description – The final flag is in English and must be wrapped in RITSEC{ }
Competition– RITSEC 2019
1. The challenge began by with 2 images. One which included a line of handwritten cryptic code and another photo of charachter on a map.

2. From this I took a screenshot of both images and google searched using those photos. From this I was able to find the character was called ‘Simic Manipulator’ which was a German card for a game. The image was also placed over a country from an old map which was ‘the German empire’. From this I was able to deduce that I was looking for a German cipher to help me decode.
3. In order find which one, I google German ciphers and then checked images to see If any language matched what was given in the image. Instantly I saw the Copiale cipher wheel which matched the language I was looking for.
4. I used the following table to assist in translating the code.

5. Once I decoded the message, I got the following output.
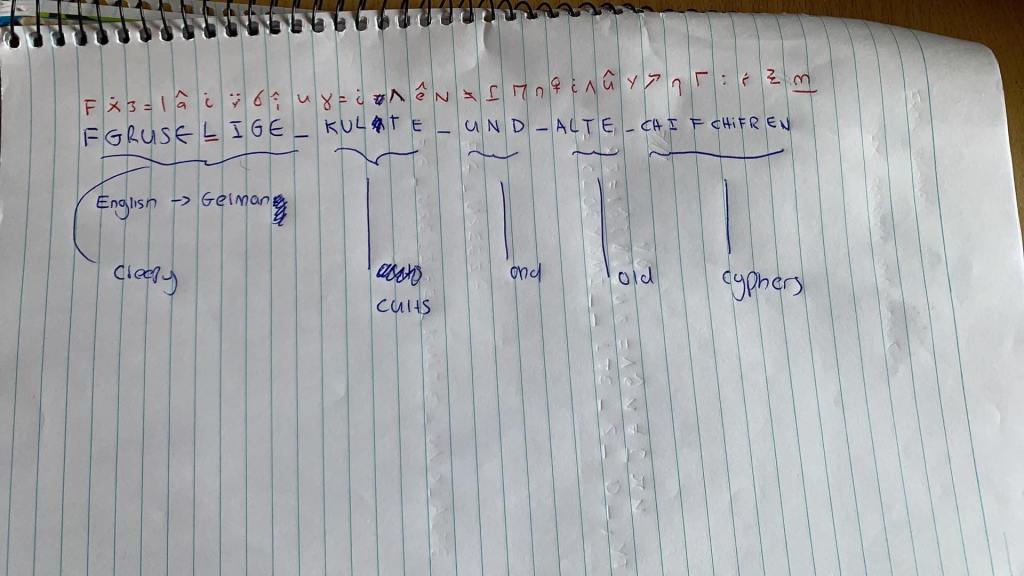
6. As the flag didn’t make sense, I tried converting some of the words to German considering the cipher was a German one. Google translated this to ‘creepy cults and old cyphers. Once wrapped in the flag, it resulted as RITSEC{creepy cults and old cyphers}.
ROT47 Challenge
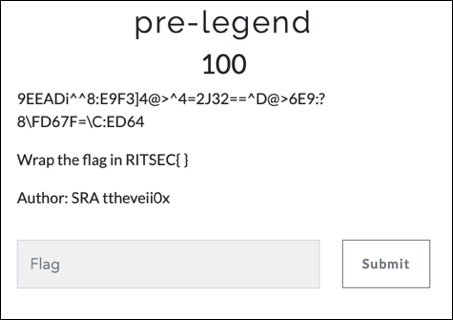
Title– Pre-Legend
Category– Cryptography
Description-9EEADi^^8:E9F3]4@>^4=2J32==^D@>6E9:?8\FD67F=\C:ED64
Wrap the flag in RITSEC{ }
Competition– RITSEC 2019
- To begin this challenge, I copied the code given to me into Google in the hopes of finding a match for characters or patterns similar to what was given to me. With no luck I then began to try in segments. I copied ‘9EEADi^^8:’ and pasted this into Google. This provided me with a match for a variety of decoder tools such as ROT5, ROT13, ROT18, ROT47.
- Reading the description for each decoder, ROT47 provided a strong similarity with a set of letters, numbers, and symbols (All ASCII characters).
- Once decoding this link, I was given a GitHub link which was the final flag.
- Wrapping this up, I received the flagRITSEC{https://github.com/clayball/something-useful-ritsec}